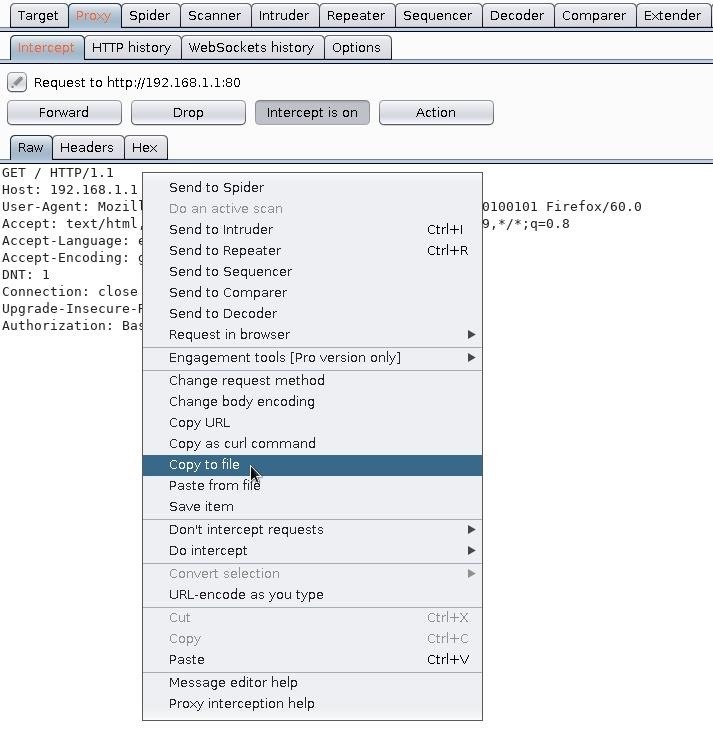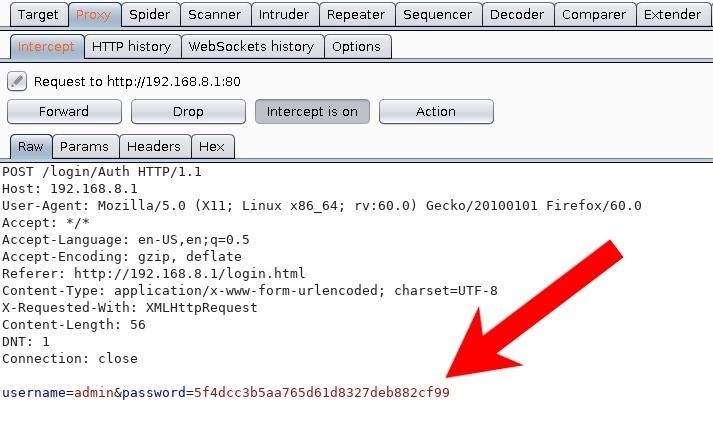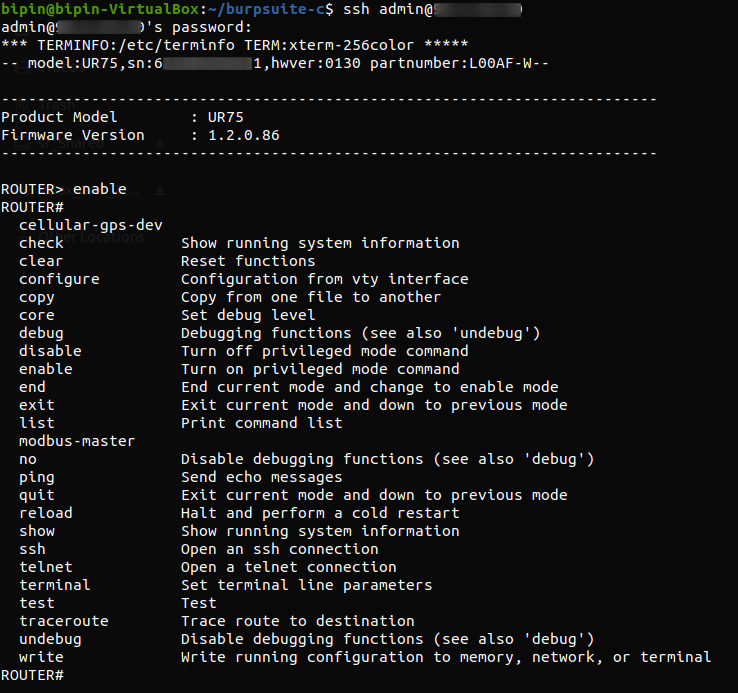
Inside the Router: How I Accessed Industrial Routers and Reported the Flaws | by Bipin Jitiya | Oct, 2023 | Medium

Inside the Router: How I Accessed Industrial Routers and Reported the Flaws | by Bipin Jitiya | Oct, 2023 | Medium

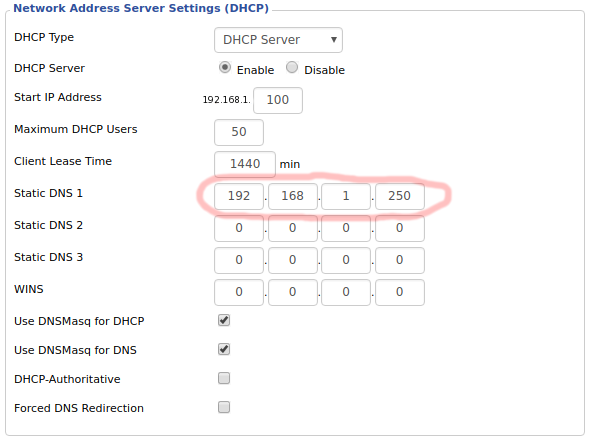
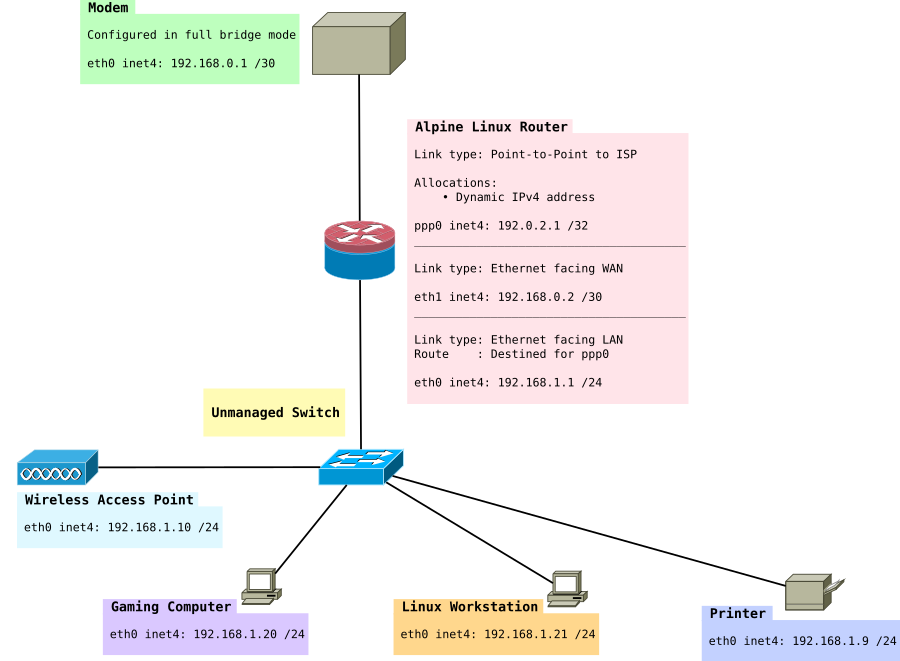
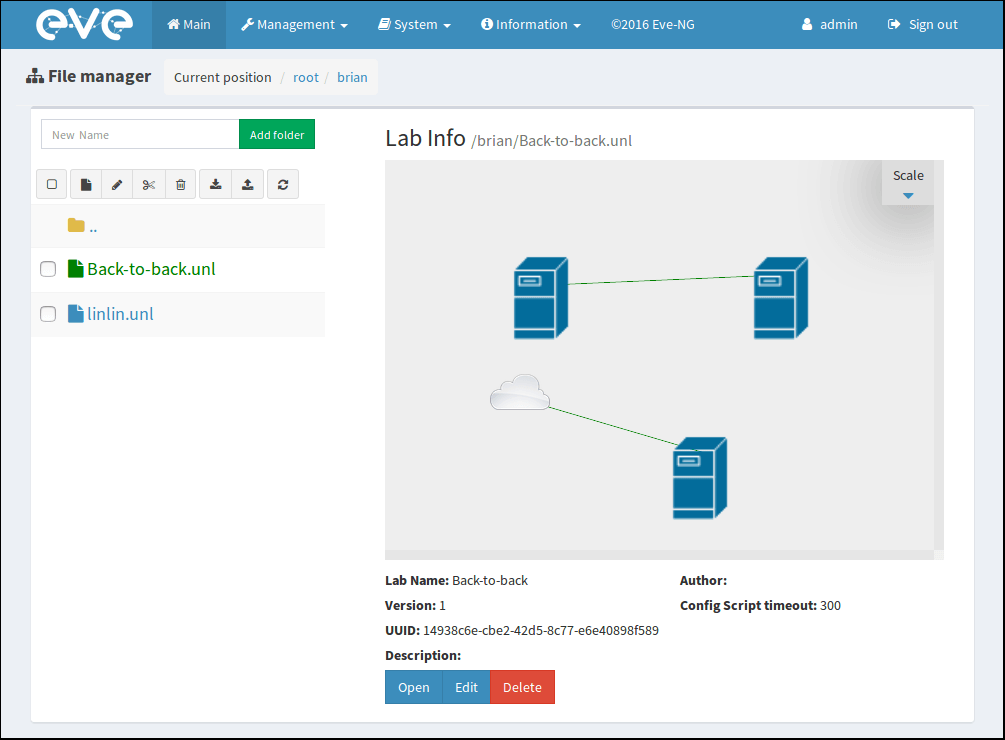
Connectivity experiments with an SAP server and client VM – Linux router, SquidMan, dnsmasq, and SSH tunnels | SAP Blogs
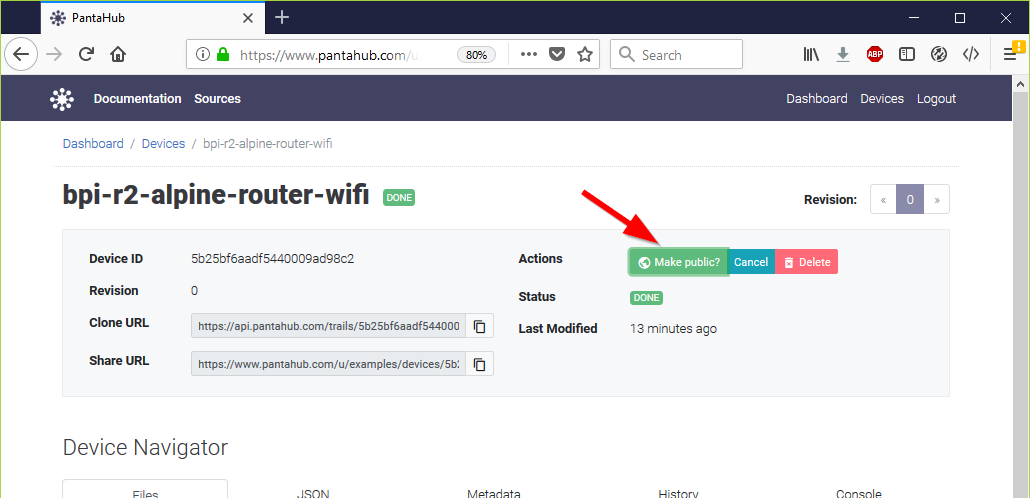
BPI-R2 new image: Basic Alpine Router Platform with WIFI AccessPoint on Pantavisor 005 (2018-06-17) - Image - banana pi single board computer open source project official forum BPI team

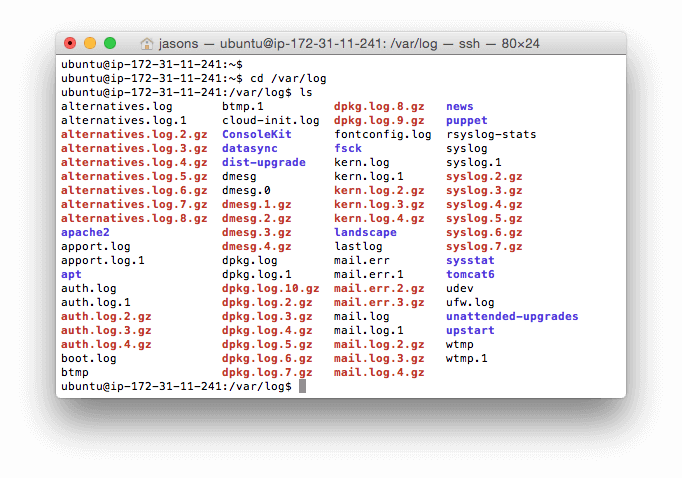




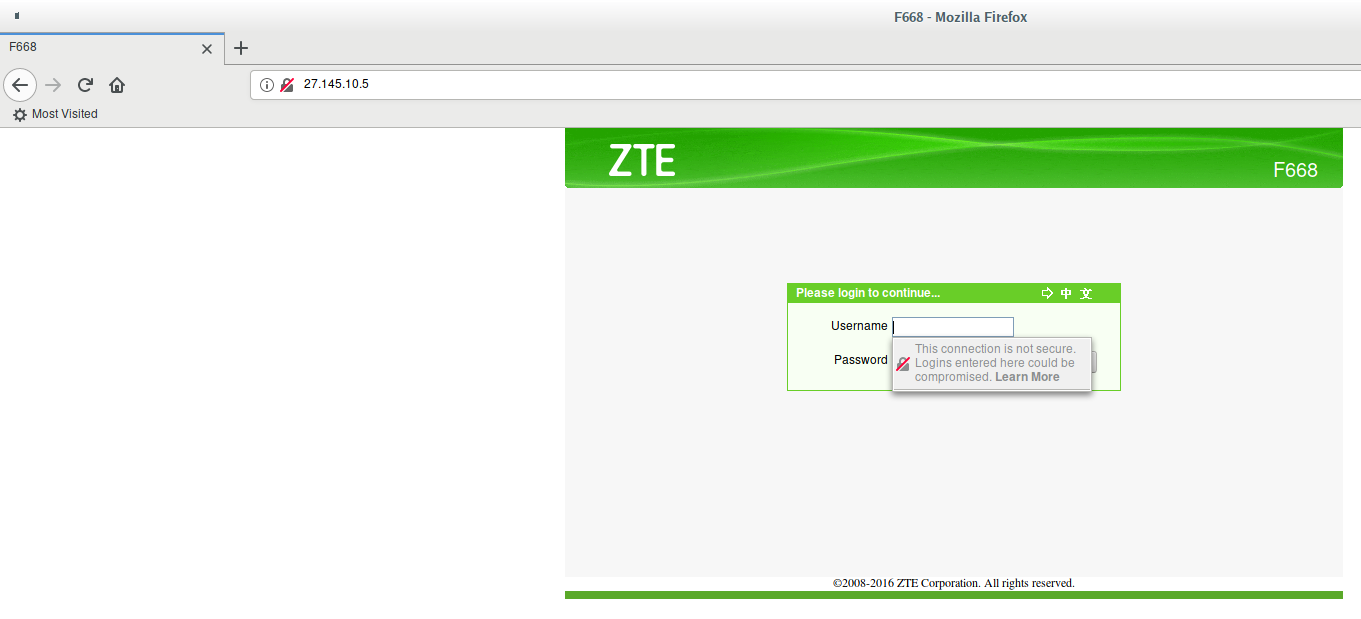
![OpenWrt Wiki] Log into your router running OpenWrt OpenWrt Wiki] Log into your router running OpenWrt](https://openwrt.org/_media/media/doc/walkthrough-password-config-5.png?w=1000&tok=aa2a78)